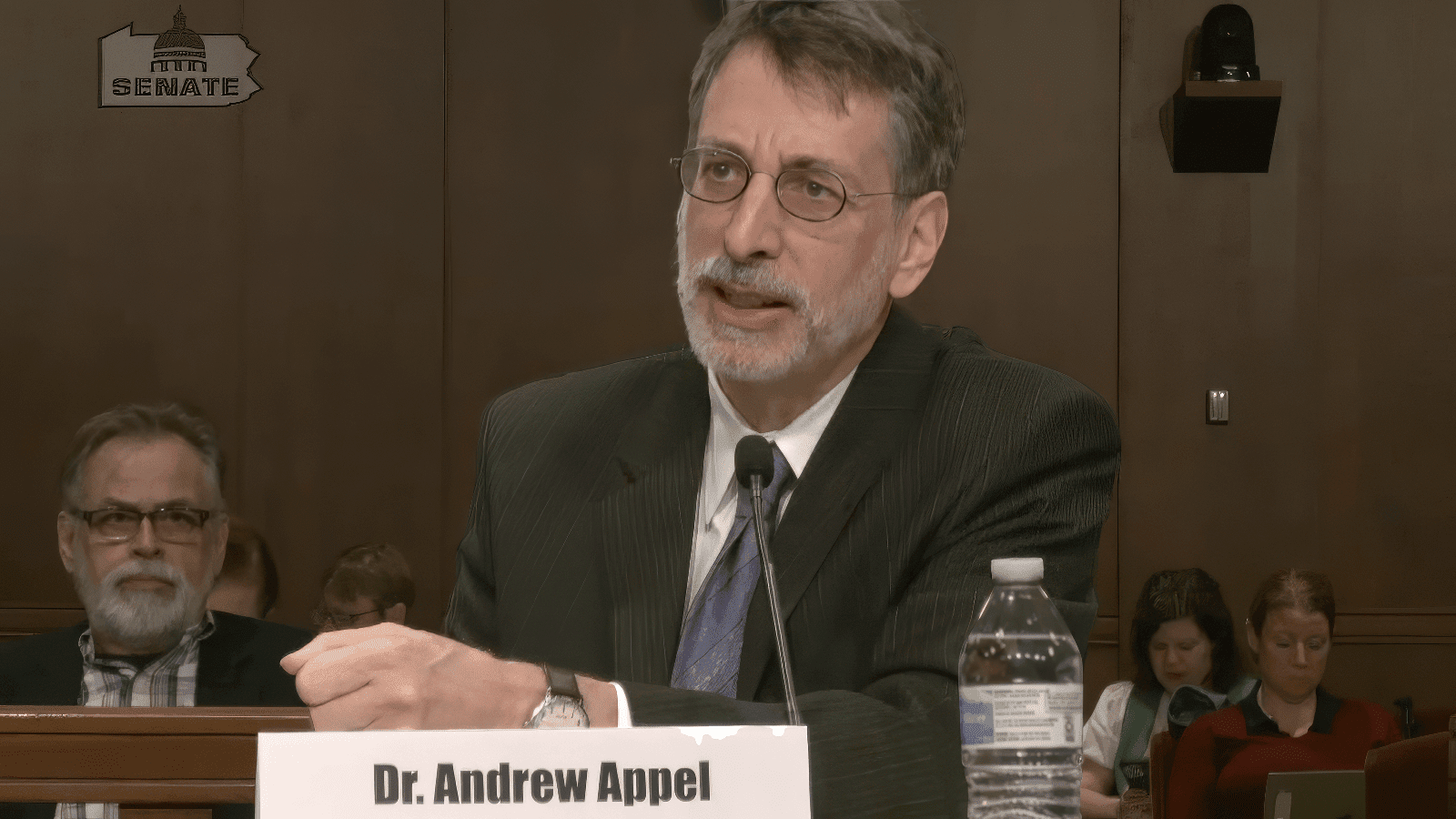
There’s been a lot of anxiety lately about the security of the American balloting infrastructure, but Andrew Appel has been thinking about this question for years. He has research specialties in public policy and security and privacy.
He has research specialties in public policy and security and privacy. He’s a well-known specialist in election technology who is often quoted in the media, and has served

Andrew Appel
as an expert witness on the subject before government committees.
He’s famous for having once shown how easy it was to reprogram a popular voting machine to play Pac-Man.
In this episode, he discusses how the pandemic has scrambled the situation for the 2020 general election, and how Americans might feel confident with the result of an election held largely by mail. He talks about which in-person voting machines are more secure than others. And he discusses the perils of Internet voting.
We recorded this podcast before the recent controversy surrounding the postal service. We encourage you to listen to this podcast, and read his recent blog post in Freedom to Tinker to bring you up to date.
Subscribe: iTunes, Spotify, Google Podcasts, Stitcher, RSS Feed
Links:
“Online and Vulnerable: Experts find nearly three dozen U.S. voting systems connected to Internet,” NBC News, Jan 10, 2020
“How to Hack an Election in Seven Minutes,” Politico, Aug. 5, 2016
Testimony to the House Subcommittee on Information Technology, Sept. 28, 2016
Transcript:
Aaron Nathans:
From the Princeton University School of Engineering and Applied Science, this is Cookies, a podcast about technology, security and privacy. On this podcast, we’ll discuss how technology has transformed our lives, from the way we connect with each other, to the way we shop, work, and consume entertainment. And we’ll discuss some of the hidden tradeoffs we make as we take advantage of these new tools. Cookies, as you know, can be a tasty snack, but they can also be something that takes your data. A lot has happened in American voting since the 2000 Florida election debacle, but have the changes created more problems than they solve?
With us today is Andrew Appel, the Eugene Higgins Professor of Computer Science with research specialties in public policy and security and privacy. Specifically, he’s a well-known expert in election technology. We recorded this episode before the recent controversy over budget cuts and policy changes at the United States postal service. This is still a relevant and fascinating conversation about voting technology vulnerabilities, including questions about voting by mail. Let’s get started. Andrew, welcome to the podcast.
Andrew Appel:
Glad to be here.
Aaron Nathans:
So, how has the pandemic scrambled the situation with voting in America as we begin to close in on the 2020 general election?
Andrew Appel:
Well, obviously it’s dangerous for crowds of voters to go into a physical traditional precinct polling place and all vote, especially if they have to touch screen equipment that other voters have been touching. It may be possible to vote safely that way, if you spaced the lines out and sanitized the pins use to mark optical scan ballots, but it seems really preferable to have people vote by mail this year. Now, in some states out West, they have mostly vote by mail or almost entirely vote by mail. So, that’s nothing new for them. But in a lot of states where maybe only five or 10% of the voters have been voting by mail, for election administrators to switch over to really large scale vote by mail is going to be a big adaptation for them that they are scrambling to get in place before November.
Aaron Nathans:
Do you think they can make that adjustment on short notice?
Andrew Appel:
I think it will be possible. They’ve had now many months of notice. That gives them time to arrange for the printing of a lot more absentee ballots than they would have expected. But of course, a lot fewer in-the-polling-place optical scan ballots. They may or may not have the equipment to really quickly scan all those ballots, but every state has equipment to scan absentee ballots. It just may take them a little longer to count all the votes in November. So, I think with enough months’ notice that they’ve had, it won’t be easy for them, but good election administrators should be on top of this.
Aaron Nathans:
We’ve heard a lot of criticism on cable news about vote by mail, that perhaps it’s unreliable, that it’s a vulnerable to fraud. I mean, is that true?
Andrew Appel:
Vote by mail doesn’t have some of the protections that you get in the polling place. For example, the concept that the voter must go into the voting booth to mark the ballot where nobody else can see what they’re doing. But in general, there doesn’t seem to be any real issue with voter fraud in vote by mail ballots. There have been occurrences in one or two states from time to time of collection and payment for absentee ballots, large scale or intimidation. Some of those people were caught and convicted. So, it’s always something you have to watch out for, but there doesn’t seem to be any really large scale systematic problem.
Aaron Nathans:
So, in general, how secure is the American balloting infrastructure? I mean, voting involves more than just the act of casting a ballot. I mean, are there different points of vulnerability in American voting?
Andrew Appel:
Before the ballot is cast you have to worry about the programming of the voting machines. Although when voters are marking a paper ballot by hand, then there’s a little less of that worry because the voter can see what’s on the paper and the scanner can see a mark, and anyone recounting that ballot can see what’s on the paper, what the voters saw. Then you have to worry about the computerized equipment that counts the ballots, whether it’s on a touch screen or the optical scanner, those are computers, they can be hacked, which is to say, some person with criminal intent could replace the software that interprets and counts the votes and make it cheat. If you hack an optical scanner to make it cheat, you can use audits to detect that problem and correct it, like a recount. A recount is a full scale audit where you look at every single paper ballot, but you can do much more efficient audits.
Look at a statistical sample of the paper ballots and get very high confidence that the results claimed by those optical scan computers actually reflect what the voters marked. For paperless touchscreen voting machines, that’s impossible. There is no paper ballot that the voters saw. You only have the word of the computer program, and if it was a fraudulent computer program, then you have to take its word. So that’s why paperless touchscreen voting machines are so dangerous. But essentially in every state, they have now realized this. There are only three or four states left that are using any significant numbers of paperless touchscreen voting machines. And even in those states election officials understand and realize that they have to get rid of those machines and replace them with something more secure as soon as possible.
And then finally, you should worry about the computers that aggregate the vote totals together from all the precincts or all of the batches of optical scan ballots, for example. But in most states it’s a good practice that the county clerk or some election official publishes their precinct by precinct tabulation of how many votes were cast for each candidate in each precinct. And the human witnesses to the tallies in each precinct can compare that with what they saw in the precinct and add it up themselves. So, there’s a way for us to audit the computerized totals to make sure that there hasn’t been any funny business this time.
Aaron Nathans:
Well, after Bush v. Gore, direct recording electronic voting machines became popular, can you tell us what those machines are? What the thinking was behind using them, and what was the flaw in that logic?
Andrew Appel:
Well, the problem that we saw in Florida in the year 2000 is that punch card ballot technologies, just a truly terrible technology. It doesn’t record the voter’s intent very well. It’s fragile, there’s so many problems with punch cards. And so, the Congress in United States in 2002 banned punch card voting in the United States. That was a good thing to get rid of. And then, many states that had been using punch cards and lever machines which were also banned rushed to do something else. And there was a good choice available. And there was what turned out to be a terrible choice available. A good choice was optical scan paper ballots. And half the states had been using that all along and continue to use optical scan paper ballots. And that’s the most secure way of voting.
The voter fills in the oval next to the names of the candidates of their choice. And that can be counted by computer. And in case the computer was hacked, you can recount it by hand. A human being can look at that same piece of paper that the voter looked at and marked and get the right count. And if a hand recount is laborious and expensive, which it is, you can do a statistical sample of recount, what’s called a risk limiting audit. But the terrible technology that some states rushed into was called, a DRE, Direct Recording Electronic voting machine. That’s a touchscreen. Voter indicates their choice on the screen, the computer inside either records their vote or records a fraudulent vote, depending on whether the legitimate software is still installed in that voting computer or whether a hacker has been able to replace it with cheating software. And there is no piece of paper that the voter marked or saw even, and that can be looked at in a recount to determine the voter’s intent.
It’s entirely, whatever computer program was in that machine on election day decides whether you’re really recording what the voter indicated or something else entirely. So that’s what many states rushed to buy in about 2003, 2004. And by 2003, 2004, computer scientists were already explaining to policymakers this basic point of computer science, that a computer does whatever program is running in it today. And on election day, how can you tell which program is running in that computer? By 2008 that point was pretty well understood. No state purchased a paperless touchscreen after 2008. And the substantial majority of the states that had been using paperless touchscreens before 2008, switched over to paper ballots, countable by computer, recountable by hand. And that’s where we were in 2019, approximately 45 states using paper ballots of some form, and approximately five states using paperless touchscreens. And I say, approximately because in many states each county gets to choose the technology it wants to use. So it’s not a whole state at a time in many cases.
Aaron Nathans:
You’re listening to Cookies, a podcast about technology, security and privacy, brought to you by the School of Engineering and Applied Science at Princeton University. We’re speaking with Andrew Appel, the Eugene Higgins Professor of Computer Science at Princeton. In our next episode, we’ll talk with Jennifer Rexford, the chair of the computer science department here at Princeton, about just how secure the internet is. But for now, let’s jump back into our conversation with Andrew Appel, in which we’ll discuss how we can feel confident of the result of an election held by mail.
So things being as they are, what’s your biggest concern aside from pandemic related issues, with the machines that people will walk in and vote with on election day?
Andrew Appel:
In a few states, they’re beginning to adopt ballot marking devices, BMDs. And these are touchscreen voting machines, where the voter indicates choices on the touchscreen and it prints out an optically scannable paper ballot, that then the voter can feed into a scanner for counting by computer and for later recounting by hand. So that seems like it should be okay, because that same piece of paper that the voter got to look at with the record of their votes on it can be recounted by human beings who see that same piece of paper. But the problem, as we discovered in about 2018, shortly after these machines came into use is two-fold. First, the vast majority of voters don’t inspect the piece of paper printed out by the ballot marking device.
Andrew Appel:
They’ve made their choices on the screen, they’ve reviewed them on the review screen of the touchscreen, the paper prints out, they’ll just carry it over to the scanner and feed it in without looking at it. And we know this from observations of real voters in real polling places. In fact, a more controlled study of real voters in a simulated polling place found that only about 7% of the voters would actually notice if the computer flipped one of their votes. So, therefore the paper ballot printed by a ballot marking device doesn’t necessarily hold the vote that the voter actually indicated. And we used to think, well, if only a few voters check their ballots carefully, at least they’ll catch it. If the machine is cheating, there’ll be a few voters who will catch it red handed and then you can do something about it. But there’s nothing you can do about it.
That voter who says, “This paper ballot doesn’t have what I indicated marked on it.” What are they supposed to do? Well, they’re supposed to raise their hand and alert the poll worker, and the poll worker is supposed to say, “Okay, that’s fine. We’ll void that one and you can do it over.” And indeed that voter won’t have their votes stolen. But all their neighbors, the 93% of voters who don’t carefully check their ballots can have their votes stolen, and a hacked fraudulent ballot marking device can steal. Instead of trying to steal 10% of the votes and shift them from one column to another, it can steal 9.3% of the votes. That’s 93% of 10%.
And you might think, but this voter caught the machine cheating red handed that’s evidence. And we should use that to, to what? To invalidate the entire election? Are you saying if a few voters raised their hands and say, “That’s not what I marked.” That the election should be invalidated? That doesn’t work. If you start doing that, then anyone can start raising their hands and claim that’s not what I marked and try and get an election invalidated. So the problem is, even if a few voters catch the machine cheating, there’s no recourse for them. And for that reason, ballot-marking devices are a really bad idea. And it’s a good thing that they’re not in use in very many states. And we should prevent other states from adopting them. It’s just bad policy. What most states do is hand mark, fill in the bubble optical scan ballots. That’s the most reliable way to vote.
Aaron Nathans:
How vulnerable are we to a situation where people vote, they submit their vote however they submit it, and then somehow a hacker goes in and changes the totals?
Andrew Appel:
That’s definitely a possibility, right? It’s not that uncommon for computer servers to be hacked into. Big companies that you would think have good security practices find themselves hacked, and county election computers are also going to be vulnerable to hacking. So, the protection we have in that case is the ability to audit and recount by hand the batches of paper ballots that the voters actually marked themselves. Because that’s a way for humans to look at the same pieces of paper that the voters marked, and there is nothing the hacker can do about that because the computer isn’t in the middle there. Full recounts are expensive. So we don’t want to do full recounts every time. We want to do statistical samples. So the concept of a risk limiting audit, is the appropriate size statistical sample of the paper ballots to make sure that what’s indicated on them by the voter’s pens is consistent with the results claimed by the computer tabulation. And a few states are now starting to do risk limiting audits or to do pilot projects of risk limiting audits to figure out the logistics and statistics of that concept.
Aaron Nathans:
What is internet voting, and is it actually happening anywhere?
Andrew Appel:
People want to do all of their life transactions on the internet, from their banking to their personal life. So, naturally people think, why can’t I vote by internet? And if it could be made secure, if we could make sure that no hacker can just choose which candidate gets elected regardless of what the voters said, then that would be a fine idea. But internet voting is not securable. Think about what happens. You run some app on your phone or your computer that gives you the appropriate ballot for you. Well, how do we know who’s you? We don’t have a system of digital credentials in this country that connects every voter registered in a certain way to their particular computer or phone. But suppose even we did. You interact with some app and you indicate which candidates you’re voting for. And the app says, “Okay, that’s what I’ve transmitted.”
And then, what if it transmits something else? The app as legitimately installed by the designer probably does that. But if it’s hacked, if a hacker manages to hack into the server, from which you download the app or into your own computer or phone, they can replace the app with a fraudulent one that says, “Okay, that’s what I’ll transmit.” And then it changes the votes and transmits something else entirely. And it’s hard enough to protect servers against that kind of hacking, but to also need to protect the millions of individual voters’ own phones and computers from that kind of hacking is impossible. So, we cannot secure internet voting. Banking we can secure, because there is an end-to-end transaction receipt for each transaction. Number one, if it appears on your bank statement something different that you didn’t authorize, you can deal with the bank about that. And there are laws protecting you.
But in this country we have the secret ballot. There must not be a provable receipt for each vote. Otherwise, people could be too easily coerced or bribed to vote a certain way. Furthermore, banks tolerate a certain percentage of fraud. A credit card company may find it cheaper to tolerate 2% of fraud rather than pay an extra 5% for the means to prevent that fraud. That’s a tradeoff that banks can make and the law permits them to make that trade off. Where is that trade off for internet voting? So, internet voting is just inherently not securable. And that’s why by and large, we don’t have internet voting in this country.
Aaron Nathans:
Is it anywhere? And is anybody seriously talking about doing it for this election?
Andrew Appel:
Some election administrators are panicking about the prospect of switching from in-person voting to vote by mail on a huge scale with only a few months to go. And there are some companies selling internet voting solutions with deceptive marketing practices claiming security when it’s inherently insecure, claiming that their systems are certified when they’re not really certified. And it’s very tempting for election administrators to seize upon this solution in this year of the pandemic, when certainly drastic measures are going to be needed. But it’s not an acceptable solution because of the ability to so easily hack internet voting at scale.
Aaron Nathans:
So, on a policy level, is there anything that you would recommend going forward that would make the voting system more secure?
Andrew Appel:
The most secure system we know of, it’s not perfect, but it’s the best we know how to do is, hand marked optical scan paper ballots that the voter marks with a pen, either in the polling place or at home and mails it in, counted by optical scan computers, which are pretty reliable and accurate when they’re not hacked. We have data about that. And in case those optical scanners are hacked, we have risk limiting audits with the ability to scale up the full recounts, to detect any possible hacking or other errors, to prove and demonstrate when there isn’t hacking when the election outcome is correct. Right? So hand marked paper ballots, optical scanners, and risk limiting audits. Now, the first two of those are in use in almost all the states. Hand marked paper ballots and optical scanners. And a few states are now doing risk limiting audits. And a lot more states are learning about that process. That’s what we need.
Aaron Nathans:
Well, last question. What are your main concerns going in to this upcoming election?
Andrew Appel:
The logistics of switching over to almost all voters voting by mail is going to be a challenge for the states where vote by mail has been restricted to only a few voters in the past. And the temptation to adopt the inherently insecure solution of internet voting seems like it may be very strong in some states.
Aaron Nathans:
Just to follow up on that. I mean, if anybody disputes the veracity of the results, how confident are you that the voting system can withstand the scrutiny needed to show a clear winner?
Andrew Appel:
In the kind of vote-by-mail situation that we’re going to likely be in most states this year, it’s important to have clear accounting for the chain of custody of those ballots as they arrive and they’re processed. You want that done in front of witnesses in a bipartisan way. It may take more time than in most years to process those ballots. We probably won’t have results in some states on election night. So the public and the media have to understand that this year we may not get the results on Tuesday night. And I think if we keep those two issues in mind, that we have paper ballots marked by the voters with a clear chain of custody and that we may need to take the time to count them accurately, we will be fine.
Aaron Nathans:
Well, I want to thank Andrew Appel, the Eugene Higgins Professor of Computer Science at Princeton, as well as our recording engineer, Dan Kearns. Cookies is a production of the Princeton University School of Engineering and Applied Science. Show notes are available at our website engineering.princeton.edu. The views expressed on this podcast do not necessarily reflect those of Princeton University. I’m Aaron Nathans, Digital Media Editor at Princeton Engineering. Watch your feed for another episode of Cookies soon, and we’ll discuss another aspect of tech security and privacy. Thanks for listening. Peace.